With a 60% surge in App Retailer submissions as builders embrace vibe coding and AI-assisted improvement instruments, Apple’s App Retailer crew has recognized an rising safety problem: what occurs when an app you obtain later evolves into one thing basically totally different — with out Apple having an opportunity to evaluate these adjustments.
Vibe coding the brand new assault floor
Let’s say you put in a easy chess app, solely to find later that it has up to date itself into one thing totally different, or that it’s downloaded exterior code that modifies or provides to what it does after set up. Some consultants already count on as a lot as 30% of latest safety exposures to be generated by unexpectedly made vibe-coded apps. That may flip into a fair larger threat as Apple is pressured to help app sideloading in some markets.
Theoretical menace?
The deeper threat is that reputable‑seeming apps might introduce unverified, remotely delivered code after set up. It is a recognized malware sample; one historic instance is XcodeGhost, a compromised model of Apple’s Xcode improvement atmosphere that contaminated apps constructed with it. Extra just lately, CovertLabs recognized 198 iOS AI apps leaking person chat historical past and personal knowledge. Even in the present day, information of the DarkSword iOS exploit exhibits that hackers see Apple’s platforms as high-value targets, which suggests any potential safety flaw will likely be explored and, if potential, exploited.
Apple protects
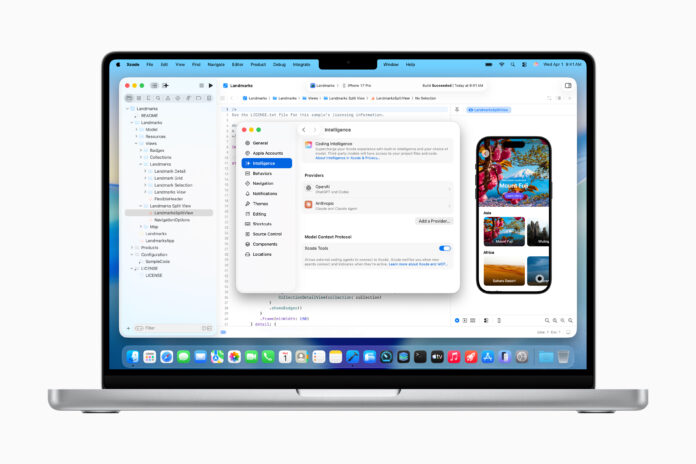
Apple’s newest response to this menace seems in an up to date set of App Retailer tips first famous by The Data. Reportedly, Apple is pushing again on “vibe coding” platforms similar to Replit and Vibecode, arguing that they violate lengthy‑standing guidelines prohibiting apps from working code that may alter how different apps behave.
The purpose isn’t to inhibit vibe coding per se, MacRumors tells us; Apple significantly objects to instruments that show newly created apps inside an embedded net view inside the app.
As an alternative, Apple needs these previews opened in an exterior browser, which prevents app‑inside‑app execution that might circumvent evaluate. I think about the transfer to open in an exterior browser would additionally place that app conduct within the extra protected Safari sandbox safety, which restricts what such apps can do to your system. Some features may fail, however permissions would stay safe.
Dynamic code and menace supply
It’s tempting to assume the priority is that these apps might bypass Apple’s fee construction. However Apple itself says the motivation is safety — stopping apps from basically altering their conduct with out evaluate.
“Vibe-coding” instruments permit customers to jot down, generate, or modify code dynamically in‑app; in doing so, they create a situation the place apps constructed utilizing them can evolve into one thing totally different after set up. Whereas that is helpful for training and experimentation, it additionally creates a sequence of potential safety vulnerabilities. For example, if a malicious actor compromised a vibe‑coding platform, they might push dangerous updates to apps developed inside it.
Apple’s developer tips already attempt to tackle this concern:
“Apps needs to be self‑contained of their bundles and will not learn or write knowledge exterior the designated container space, nor might they obtain, set up, or execute code which introduces or adjustments options or performance of the app, together with different apps. Academic apps designed to show or permit college students to check executable code might, in restricted circumstances, obtain code, offered that such code just isn’t used for different functions and is absolutely viewable and editable by the person.”
To my thoughts, the intent is to mitigate in opposition to Trojan‑horse‑model assaults that is perhaps enabled by unreviewed code execution.
Apple’s App Retailer can not turn out to be a backdoor
In the long run, even if Apple does now help GenAI-boosted workflows in Xcode, it doesn’t need the App Retailer to turn out to be a conduit for the distribution of apps that may fetch or execute unreviewed code after approval. In any case, if each app did this, the worth of app curation is itself diminished. Whereas it is perhaps that different app marketplaces select to permit such flexibility (good luck with that), Apple has no intention of allowing the App Retailer to serve that position.
In November, Apple strengthened its App Assessment tips with a brand new rule to forestall app impersonation. “You can’t use one other developer’s icon, model, or product title in your app’s icon or title with out approval,” that rule stated.
Apple’s concern is that dynamic code‑era instruments make it simpler for builders (or attackers) to construct, deploy, and ship copycat apps or apps that may be up to date utilizing unknown instruments, frameworks, or distant code after set up. Generative AI (genAI) additional accelerates this threat by making it trivial to provide complicated code rapidly. That is actually contributing to the roughly 2.28 million apps now out there on the App Retailer, which is up by 160,000 from the 12 months earlier than.
Worry, uncertainty, doubt — and alternative
The menace the App Retailer crew needs to guard us from is a pure extension of the proliferating AI-driven challenges we’re already experiencing in our lives. Simply as we now scrutinize AI‑generated pictures of world leaders in espresso retailers for inform‑story indicators of additional fingers, we might quickly have to query whether or not the apps on our units are actually what they declare to be. Plus, after all, as criminals establish frequent code signatures in vibe‑generated apps, they could but establish enticing new assault surfaces nobody else has come throughout but.
That’s not hyperbole — we all know we dwell in fascinating occasions. There is no such thing as a doubt that on the subject of apps doing issues on our digital units that include a lot of our personal private knowledge, it’s much better to play protected and deploy tactically than transfer quick and break extra of the few remaining issues we’ve left.
You’ll be able to observe me on social media! Be a part of me on BlueSky, LinkedIn, and Mastodon.