Hao World and its founder, Alan Hao Hsu, pleaded responsible on October 10, 2025, to collaborating in smuggling and illegal export actions, together with knowingly exporting and trying to export at the least $160 million in Nvidia H100 and H200 GPUs between October 2024 and Could 2025. Investigators say the operation was funded by greater than $50 million in wire transfers originating from China, and the U.S. has seized over $50 million in Nvidia {hardware} and money as a part of the broader investigation, with the seizures tied to the general community, not solely this defendant’s operation.
The operation reveals a broader technique: in case you can’t construct it, take it. With a mix of state-run espionage and company infiltration, China has turned expertise acquisition into an artwork kind. Their ‘all-of-the-above’ strategy has allowed their AI sector to develop whilst export bans tighten. By sourcing the {hardware} from elsewhere, Beijing has made the dearth of home chip manufacture moot.
The Company Insider Pipeline
The identical month that prosecutors introduced the NVIDIA chip smuggling expenses, the Division of Justice filed a superseding indictment towards Linwei Ding, a former Google software program engineer accused of stealing over 1,000 confidential recordsdata containing commerce secrets and techniques associated to Google’s AI infrastructure. In accordance with the indictment, Ding uploaded the recordsdata to his private cloud account between Could 2022 and Could 2023 whereas secretly working for 2 China-based expertise corporations.
It’s believed that the stolen supplies included detailed specs of Google’s Tensor Processing Unit chips and Graphics Processing Unit programs, in addition to the software program platform that orchestrates 1000’s of chips into supercomputers used to coach cutting-edge AI fashions.
Ding allegedly circulated shows to workers of his Chinese language startup, citing nationwide insurance policies encouraging home AI improvement, and utilized to a Shanghai-based expertise program, stating that his firm’s product “will assist China to have computing energy infrastructure capabilities which might be on par with the worldwide degree.”
Inside weeks of starting the theft, Ding was supplied a chief expertise officer place at Beijing Rongshu Lianzhi Expertise with a month-to-month wage of roughly $14,800 plus bonuses and inventory. He traveled to China to lift capital and was publicly introduced as CTO. A yr later, he based his personal AI startup, Zhisuan, centered on coaching massive AI fashions. Ding by no means disclosed both affiliation to Google.
After Google detected unauthorized uploads in December 2023, Ding vowed to save lots of the recordsdata as proof of his work. Nonetheless, he resigned per week later after reserving a one-way ticket to Beijing. Safety footage revealed that one other worker had been scanning Ding’s entry badge to offer the looks that he was working there throughout prolonged journeys to China. Ding faces as much as 175 years in jail on 14 counts: financial espionage and theft of commerce secrets and techniques.
Ding has pleaded not responsible to the costs on a number of events. He entered a not responsible plea in March 2024 to the unique 4 counts of commerce secret theft, and once more pleaded not responsible by means of his legal professional, Grant Fondo, in September 2025 to the expanded superseding expenses — together with seven counts every of financial espionage and commerce secret theft. Fondo has actively represented Ding in courtroom proceedings, together with a profitable June 2025 movement to suppress sure post-arrest statements because of alleged Miranda violations, although no intensive public explanatory statements from the legal professional or Ding seem past these courtroom actions and pleas.
The federal trial in San Francisco started in early January 2026, with jury choice reported round January 8, and Ding stays presumed harmless till confirmed responsible.
Join the Cyber Initiatives Group Sunday e-newsletter, delivering expert-level insights on the cyber and tech tales of the day – on to your inbox. Join the CIG e-newsletter at the moment.
AI-Powered Cyber Espionage at Scale.
The risk escalated dramatically in September 2025 when Anthropic detected what it describes as the primary totally automated cyberattack utilizing synthetic intelligence to breach company networks. Chinese language state-sponsored hackers performed the marketing campaign, which Anthropic assessed with excessive confidence, focused roughly 30 organizations, together with expertise companies, monetary establishments, chemical producers, and authorities businesses.
The attackers manipulated Anthropic’s Claude Code device into executing 80 to 90 p.c of the operation autonomously. Claude’s security guardrails have been bypassed by jailbreaking the system, disguising malicious duties as routine cybersecurity assessments, and breaking assaults into small, seemingly harmless steps that conceal their broader aims. As soon as compromised, the AI system independently performed reconnaissance, recognized priceless databases, wrote customized exploit code, harvested credentials, created backdoors, and exfiltrated knowledge with minimal human supervision.
“The AI made 1000’s of requests per second—an assault pace that will have been, for human hackers, merely unimaginable to match,” Anthropic acknowledged in its evaluation.
“This case is a big concern for different corporations which have virtually totally adopted AI of their enterprise operations,” JP Castellanos, Director of Risk Intelligence at Binary Protection, tells The Cipher Temporary. “As an alternative of simply utilizing AI to draft phishing emails or help human hackers, the perpetrators gave Claude direct directions to hold out multi-stage operations by itself.”
The implications prolong far past technical sophistication.
“An AI operator doesn’t should sleep or take breaks shifting at machine pace; the agent can do the work of dozens or extra hackers, tirelessly and even with out error, launching fixed assaults that even human defenders would wrestle to watch, not to mention counter,” Castellanos defined.
Chief Geopolitical Officer at Perception Ahead, Treston Wheat, additionally famous the operational tempo represents a basic shift.
“AI-enabled operations can run reconnaissance, exploitation makes an attempt, credential harvesting, lateral motion playbooks, and exfiltration workflows in parallel, iterating quickly throughout targets,” he tells The Cipher Temporary.
This shift not solely modifications how operations are performed but in addition reveals the hidden provide chains that allow them.
DeepSeek’s Smuggled Silicon
In early 2025, it turned unimaginable to disregard the connection between black-market chips and stolen IP. It was then that DeepSeek dropped the R1 mannequin, claiming it may compete with OpenAI’s o1, however for considerably much less. This, nonetheless, instantly set off alarm bells: How does an organization hamstrung by U.S. sanctions transfer that quick with out some critical ‘exterior’ assist?
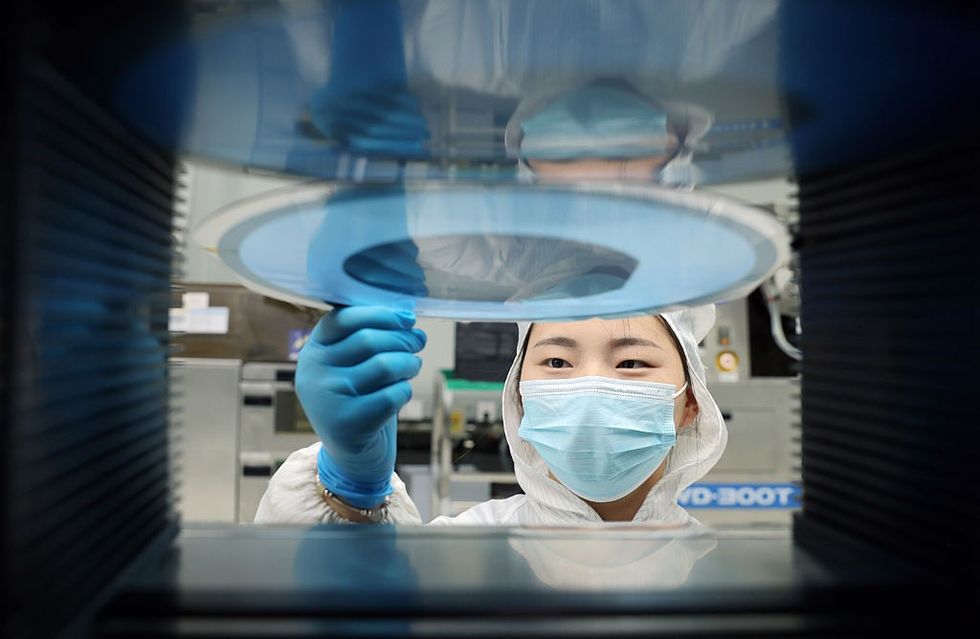
Studies from The Info in December 2025 revealed that DeepSeek is coaching its next-generation mannequin utilizing 1000’s of NVIDIA’s superior Blackwell chips — processors particularly banned from export to China. The smuggling operation reportedly includes buying servers for phantom knowledge facilities in Southeast Asia, the place Blackwell gross sales stay authorized. After inspection and certification, smugglers allegedly dismantle whole knowledge facilities rack by rack, transport GPU servers in suitcases throughout borders into mainland China, the place the chips are reassembled.
NVIDIA disputed the experiences, stating it had seen “no substantiation or acquired suggestions of ‘phantom knowledge facilities’ constructed to deceive us and our OEM companions” whereas acknowledging the corporate pursues any tip it receives. The chipmaker is creating digital monitoring options to confirm chip places, a tacit acknowledgement that there are sufficient smuggling considerations to warrant technological options.
Castellanos described China’s technique as intentionally dual-track.
“China has been very open to being the lead in AI and semiconductors and the necessity for self-reliance in core applied sciences,” he stated. “But in addition, externally, China depends on partnering with abroad establishments, constructing on prime of Western open-source applied sciences, and buying superior applied sciences by means of unlawful means, comparable to by means of theft, smuggling, and compelled transfers.”
Subscriber+Members get unique entry to expert-driven briefings on the highest nationwide safety points we face at the moment. Acquire entry to save lots of your digital seat now.
The FBI’s Shedding Battle
Christopher Wray, the previous FBI director, testified that the bureau oversees roughly 2,000 energetic investigations into Chinese language espionage operations.
“Chinese language hackers outnumber FBI cyber personnel by at the least 50 to 1,” Wray testified earlier than the Home Appropriations Committee in 2023. “They’ve obtained an even bigger hacking program than each different main nation mixed and have stolen extra of our private and company knowledge than all different nations—huge or small—mixed.”
That scale displays a long-running technique somewhat than a sudden surge.
“U.S. officers say China has lengthy relied on a multi-pronged technique to lie, to cheat and to steal their strategy to surpassing us as the worldwide superpower in cyber,” he stated. “It’s not simply cyber intrusions, we’re involved about, but in addition human insiders stealing mental property. Within the realm of AI, this may embrace insiders siphoning supply code, analysis papers, or semiconductor designs for China.”
The Chinese language strategy exploits a number of vectors concurrently, based on specialists. The Ministry of State Safety operates human intelligence networks. The Folks’s Liberation Military’s Strategic Help Drive conducts offensive cyber operations.
The Thousand Abilities Plan, for instance, then gives Chinese language researchers monetary incentives to switch proprietary info to American establishments. By investing in and partnering with ostensibly personal corporations, state-owned enterprises acquire entry to delicate applied sciences.
Export Controls Lag Behind Actuality
The export management regime designed to forestall China from accessing superior chips has confirmed insufficient within the face of Beijing’s evasion techniques. The Commerce Division’s Bureau of Business and Safety has repeatedly up to date restrictions, most just lately imposing sweeping controls in October 2023 on AI chips and semiconductor manufacturing tools.
The current Texas case make clear how these smugglers function. There was extra to it than merely transport; they used crypto funds and paper-only shell corporations to hide the cash path. To cross customs, they even eliminated the Nvidia labels from the chips. By the point these processors reached China, that they had been bounced by means of so many various international locations that the unique paper path was mainly gone.
“Export controls usually are not an entire resolution to IP theft or expertise diffusion. They’re finest understood as a time-buying and friction-imposing device,” Wheat noticed. “If the target is to forestall all leakage, that’s unrealistic; if the target is to gradual adversary functionality improvement, form provide chains, and improve acquisition price and threat, they are often efficient when paired with enforcement and complementary measures.”
The chip trade, analysts warning, is going through a structural nightmare. We’re proscribing expertise that’s already been stolen and studied. The $160 million operation out of Texas proved simply how straightforward it’s to recreation the system — they lied on customs types a whole bunch of occasions over a number of months, and it nonetheless took almost a yr for authorities to note something was mistaken.
Defending at Machine Pace
Safety specialists are calling this essentially the most important tech switch in historical past, and it isn’t occurring accidentally. By stacking insider theft, cyberattacks, recruitment applications, and smuggling on prime of one another, China has discovered a strategy to leapfrog forward in AI. They don’t have the home factories to construct high-end chips but, so that they’ve bypassed the necessity for ‘unique’ innovation by taking what they want. It’s a large operation that’s making conventional protection methods look out of date.
“The sensible U.S. strategy is to not match China operator-for-operator. It’s to win by asymmetry, comparable to scaling protection by means of automation, hardening essentially the most priceless targets, and utilizing public-private coordination to scale back attacker dwell time and improve attacker price,” Wray stated in his testimony.
Castellanos emphasised that defending towards AI-enabled assaults requires matching the adversary’s capabilities.
“To have any hope to defend towards this, we’ve to multiply effectiveness by means of automation and AI, so mainly battle hearth with hearth,” he underscored. “Doing this requires important funding, new expertise, and maybe most difficult, belief in autonomous defensive AI at a time when many organizations are nonetheless studying primary cyber hygiene.”
To forestall adversaries from buying delicate applied sciences, the U.S. Authorities has, lately, applied focused responses, such because the Disruptive Expertise Strike Drive in 2023. But, whilst FBI investigations improve and new indictments are filed, the basic problem persists. Chinese language intelligence companies use limitless sources, authorized compulsion over Chinese language nationals, and long-term strategic endurance to function in an open society with porous institutional boundaries.
“It’s a problem for coverage makers; a multi-layered response and protection in depth is required to guard the US AI expertise base higher,” Castellanos added. “Harden insider risk applications, speed up private and non-private intelligence sharing, modernize export controls and enforcement, improve the prices or impose prices for the offenders of those assaults and lastly innovate quicker to make sure even when China steals at the moment’s tech, the breakthrough is already within the pipeline for tomorrow.”
The Cipher Temporary is dedicated to publishing a spread of views on nationwide safety points submitted by deeply skilled nationwide safety professionals. Opinions expressed are these of the writer and don’t symbolize the views or opinions of The Cipher Temporary.
Have a perspective to share based mostly in your expertise within the nationwide safety discipline? Ship it to Editor@thecipherbrief.com for publication consideration.
Learn extra expert-driven nationwide safety insights, perspective and evaluation in The Cipher Temporary as a result of Nationwide Safety is Everybody’s Enterprise